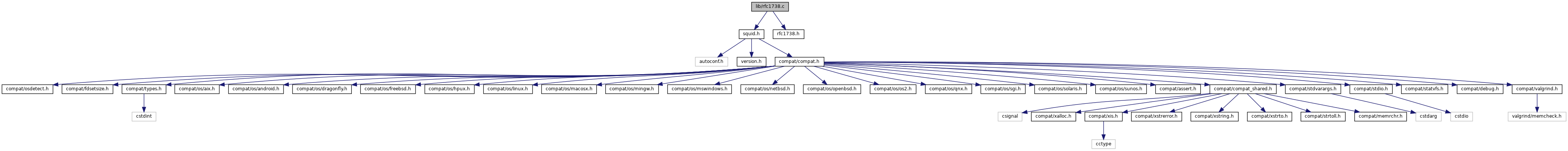
Go to the source code of this file.
Functions | |
| char * | rfc1738_do_escape (const char *url, int flags) |
| static int | fromhex (char ch) |
| void | rfc1738_unescape (char *s) |
Variables | |
| static char | rfc1738_unsafe_chars [] |
| static char | rfc1738_reserved_chars [] |
Function Documentation
◆ fromhex()
|
static |
Definition at line 130 of file rfc1738.c.
Referenced by rfc1738_unescape().
◆ rfc1738_do_escape()
| char* rfc1738_do_escape | ( | const char * | url, |
| int | flags | ||
| ) |
RFC 1738 URL-escaping
Public API is formed of a triplet of encode functions mapping to the rfc1738_do_encode() engine.
ASCII characters are split into four groups:
- SAFE Characters which are safe to occur in any URL. For example A,B,C
- CTRLS Binary control codes. Dangerous to include in URLs.
- UNSAFE Characters which are completely usafe to occur in any URL. For example; backspace, tab, space, newline.
- RESERVED Characters which are reserved for special meaning and may only occur in certain parts of a URL.
Returns a static buffer containing the RFC 1738 compliant, escaped version of the given url.
- Parameters
-
flags RFC1738_ESCAPE_CTRLS Encode the blatantly dangerous binary codes. flags RFC1738_ESCAPE_UNSAFE Encode printable unsafe characters (excluding CTRLs). flags RFC1738_ESCAPE_RESERVED Encode reserved characters. flags RFC1738_ESCAPE_ALL Encode all binary CTRL, unsafe and reserved characters. flags RFC1738_ESCAPE_NOSPACE Ignore the space whitespace character. flags RFC1738_ESCAPE_NOPERCENT Ignore the escaping delimiter ''.
Definition at line 56 of file rfc1738.c.
References NULL, RFC1738_ESCAPE_CTRLS, RFC1738_ESCAPE_NOPERCENT, RFC1738_ESCAPE_NOSPACE, RFC1738_ESCAPE_RESERVED, RFC1738_ESCAPE_UNSAFE, rfc1738_reserved_chars, rfc1738_unsafe_chars, xcalloc(), and xfree.
Referenced by AnyP::Uri::cleanup(), Ftp::Gateway::parseListing(), and TestRfc1738::testUrlEncode().
◆ rfc1738_unescape()
| void rfc1738_unescape | ( | char * | url | ) |
Unescape a URL string according to RFC 1738 specification. String is unescaped in-place
Definition at line 146 of file rfc1738.c.
References fromhex().
Referenced by ftpReadType(), Ftp::Gateway::loginParser(), main(), AnyP::Uri::parse(), parse_peer(), Helper::Reply::parseResponseKeys(), TestRfc1738::PercentZeroNullDecoding(), and TestRfc1738::testUrlDecode().
Variable Documentation
◆ rfc1738_reserved_chars
|
static |
Definition at line 41 of file rfc1738.c.
Referenced by rfc1738_do_escape().
◆ rfc1738_unsafe_chars
|
static |
Definition at line 20 of file rfc1738.c.
Referenced by rfc1738_do_escape().
Introduction
- About Squid
- Why Squid?
- Squid Developers
- How to Donate
- How to Help Out
- Getting Squid
- Squid Source Packages
- Squid Deployment Case-Studies
- Squid Software Foundation
Documentation
- Quick Setup
- Configuration:
- FAQ and Wiki
- Guide Books:
- Non-English
- More...
Support
- Security Advisories
- Bugzilla Database
- Mailing lists
- Contacting us
- Commercial services
- Project Sponsors
- Squid-based products
